
Samuel Smith spent years writing songs with a guitar in his hands.…
Read More
Samuel Smith spent years writing songs with a guitar in his hands.…
Read More
Palo Alto Networks has warned that a recently disclosed medium-severity security flaw impacting PAN-OS and Prisma Access has come under active exploitation in the wild. The vulnerability, tracked as C…
Read More
Researchers have uncovered a previously undocumented Russian group that makes extensive use of large language models (LLMs) in its attacks against private, government, and military organizations in Uk…
Read More
Microsoft and a prominent cybersecurity researcher have gotten into a very public and rather personal exchange of unpleasantries about what responsible cybersecurity disclosures should mean in 2026. A…
Read More
The Pentagon’s new $9.7 billion contract with Dell is raising questions about potential conflicts of interest after President Trump touted the company’s products and purchased significant amounts of i…
Read More
Jeff Bezos' Blue Origin is assessing damage to its launch pad after a rocket exploded during a test firing, creating a giant orange fireball seen and felt for miles around.…
Read More
A Massachusetts woman has been fired from her job at a credit union after posting a TikTok video that appeared to pray for former Attorney General Pam Bondi to suffer a severe case of throat cancer, s…
Read More
Cybersecurity researchers have disclosed details of a vulnerability in OpenAI ChatGPT that leverages the artificial intelligence (AI) assistant's implicit trust in Markdown links and images to trigger…
Read More
As AI agents become more numerous and more communicative, keeping track of where to find them is becoming increasingly important. Numerous proprietary agent registries are on the market, but the Linux…
Read More
Researchers in Switzerland claim to have built a perfect random number generator from two quantum superconducting chips, a 30-meter-long pipe, and some software. The resulting device could be used to …
Read More
Ohio Gov. Mike DeWine (R) suspended the state's tax exemption for new data centers, which has drawn developers of the power facilities to the Buckeye State amid the boom of artificial intelligence. De…
Read More
An unknown threat actor has been observed using a large language model (LLM) agent to conduct post-compromise actions after obtaining initial access following the exploitation of a publicly-accessible…
Read More
Mike Frank, the deputy chief technology officer at the U.S. Department of the Navy, joins the show to talk about the future of American naval power, the role of unmanned surface vessels, and much more…
Read More
Each vulnerability was published with working proof-of-concept code to the Microsoft-owned code repository GitHub, making them immediately available to both attackers and security professionals.…
Read More
A fake IMF email promises $4.5 million but uses pressure and urgency to steal identity documents. Learn the red flags and how to protect yourself.…
Read More
A Russian attack drone hit the roof of an apartment building in southeastern Romania on Friday, according to Romanian authorities, sharply increasing tensions between the NATO member and Moscow.…
Read More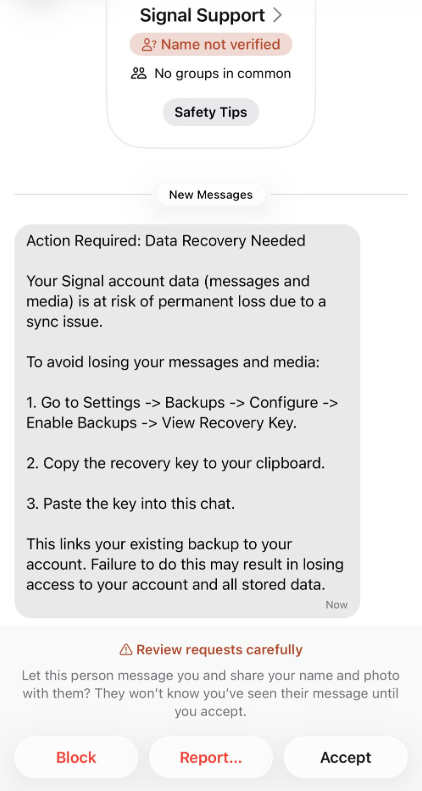
Cybercriminals are impersonating Signal Support to steal backup recovery keys, giving them access to victims' entire message archives.…
Read More
Hyundai reportedly plans to deploy over 25,000 Boston Dynamics Atlas humanoid robots across U.S. auto plants, starting at its Georgia facility in 2028.…
Read More
A previously undocumented threat actor dubbed GREYVIBE has been attributed to ongoing and persistent attacks targeting Ukraine and Ukraine-related entities since at least August 2025. GREYVIBE, per Wi…
Read More
The ability of adversaries to use commercial location data from smartphones to find and target U.S. troops in the Middle East is a "five-alarm fire" that demands immediate action, a group of bipartisa…
Read More
Shadow AI used to mean employees pasting things they shouldn't into ChatGPT. It now means something bigger: employees building full applications with AI, wiring them into production systems, and publi…
Read More
Two arbitrary code execution vulnerabilities in Notepad++ let local attackers run commands of their choice on Windows machines by tampering with the editor’s XML configuration files, with both flaws r…
Read More
Cybersecurity researchers have discovered a malicious NuGet package that masquerades as a C# software development kit for Sicoob, one of Brazil's largest cooperative financial systems, to siphon clien…
Read More
Ransomware operators have spent years refining the art of locking files. Now, some are working harder to get those lockers to every reachable system first. Microsoft’s recent warning of the Gentlemen …
Read More
In 2023, the Securities and Exchange Commission (SEC) required public companies to include a new section in their 10-K annual filings that is devoted to cybersecurity. This section is meant to address…
Read More
Big tech firms continue to push back against fines levied for alleged violations of European data protection law, in what could be a harbinger for AI regulations to come. While lawyers and experts qui…
Read More
The North Korean state-sponsored threat actor known as Kimsuky (aka Velvet Chollima) has been attributed to a fresh set of cyber attacks targeting South Korean military and corporate entities through …
Read More
CAPE CANAVERAL, Fla. (AP) — A rocket belonging to Jeff Bezos' Blue Origin exploded during a test at the launch pad Thursday night, shaking nearby homes and briefly painting the sky orange. Blue Origin…
Read More
A Medicare and Centrelink office sign is seen at Bondi Junction in Sydney, Australia, on March 21, 2016. (Matt King/Getty Images)…
Read More
A rocket belonging to Jeff Bezos' Blue Origin exploded during a test at the launch pad Thursday night, shaking nearby homes and briefly painting the sky orange.…
Read More
Open source code is everywhere in the enterprise; it’s estimated that upwards of 90% of Fortune 500 companies have it in their software supply chains. But open source code is notoriously rife with vul…
Read More
A newly discovered and so far unpatched critical vulnerability in the open source Gogs Git service not only demands immediate action from developers to secure their code, it also puts a spotlight on t…
Read More
The White House is mocking the idea of the U.S. retaining secrets involving alien encounters by launching a space-themed website that touts the arrests of immigrants unauthorized to live in the U.S. T…
Read More
An Italian Google employee is facing federal charges in the U.S. for insider trading, accused of using company information to make money on Polymarket.…
Read More
"Innerspace: Limited Edition" brings Joe Dante, Dennis Quaid, Martin Short and Oscar-winning Industrial Light and Magic effects to 4K with rich extras.…
Read More
Anthropic raked in $65 billion from investors at a $965 billion valuation in its latest funding round, overtaking OpenAI’s most recent valuation as the two AI startups race to go public. The company a…
Read More
The FBI issued a warning Thursday, stating malicious cyber actors are spoofing FIFA websites ahead of the 2026 FIFA World Cup. According to the FBI, the threat actors create websites that resemble mos…
Read More
The Fox News AI Newsletter gives readers the latest AI technology advancements, covering the challenges and opportunities AI presents.…
Read More
Ozzy Osbourne's family has partnered with tech companies to create an AI avatar of the rock star that will be able to speak with fans and appear in holograms in the U.S. and the United Kingdom this su…
Read More
A critical security vulnerability has been disclosed in Gogs, a popular open-source self-hosted Git service, that allows an authenticated user to execute arbitrary code under certain conditions. The s…
Read More
A 7-Eleven data breach linked to franchisee records reportedly exposed personal details including names, addresses, dates of birth and phone numbers.…
Read More
Cab-less electric autonomous trucks from Einride will operate on Ohio public roads this summer, moving freight between EASE Logistics warehouses.…
Read More
Threat actors are continuing to exploit a critical, now-patched security flaw impacting FortiClient Endpoint Management Server (EMS) deployments to deliver credential-stealing malware. "The campaign a…
Read More
The Commodity Futures Trading Commission (CFTC) asked a judge Wednesday to throw out a Biden-era settlement with Gemini, the cryptocurrency exchange founded by billionaire investors Tyler and Cameron …
Read More
The Treasury Department launched a new app Thursday corresponding to its investment accounts for kids, dubbed "Trump Accounts." “The Trump Administration is taking another step forward in expanding op…
Read More
YouTube is rolling out a new system to automatically detect whether generative AI was used in a video, then apply a label if needed.…
Read More
The company said the threat actor gained access to a limited portion of its IT environment last month after compromising an employee account. By the end of April, Carnival determined that the attacker…
Read More
Microsoft has come out strongly in favor of Coordinated Vulnerability Disclosure (CVD), urging the research community to share their findings and give affected vendors an opportunity to better underst…
Read More
Prosecutors said the man spent years using fake online identities to contact children and manipulate them into sending sexually explicit images and videos.…
Read More
Every time you think the industry has finally stopped doing some reckless, low-effort crap, somebody spins up a fresh box full of sketchy loaders, fake installers, recycled social-engineering bait, an…
Read More
Cybercriminals have registered more than 4,300 fraudulent domains impersonating FIFA's official web presence since August 2025.…
Read More
Government agencies are eyeing advancements in air transportation over the next decade: electric planes and fully autonomous flight.…
Read More
Anne Keast-Butler, director of GCHQ, said Russia's actions have prompted the agency to defend subsea cables and energy pipelines in British waters, disrupt Russian networks smuggling sanctioned techno…
Read More
India’s cybersecurity agency, CERT-In, has urged organizations to patch, mitigate, or isolate known exploited vulnerabilities affecting internet-facing “crown jewel” systems within 12 hours where feas…
Read More
Taking down a sprawling malware operation once signaled progress in securing the open-source ecosystem. Now, it barely registers. The GlassWorm campaign disruption comes at a moment when attackers can…
Read More
The Space Force must plan to deploy troops on orbiting space stations and at bases on the moon to prevent China from winning the new space race and controlling outer space, according to a report by an…
Read MoreCruise giant Carnival has suffered yet another data breach, with ShinyHunters claiming to have stolen personal data affecting nearly 6 million people.…
Read More
State of AI Usage Report 2026 (full report here) by LayerX Security reveals the extent of the enterprise AI visibility gap and why most organizations still don't understand where their AI exposure is …
Read More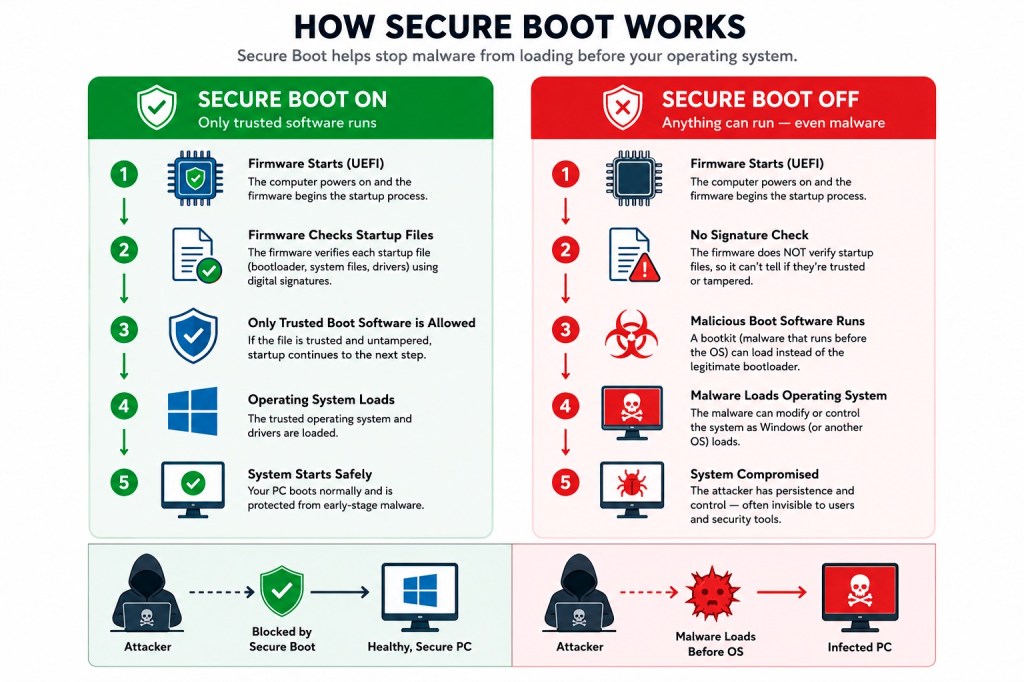
Windows is replacing old Secure Boot certificates, and some older PCs could miss future security protections if the update fails.…
Read More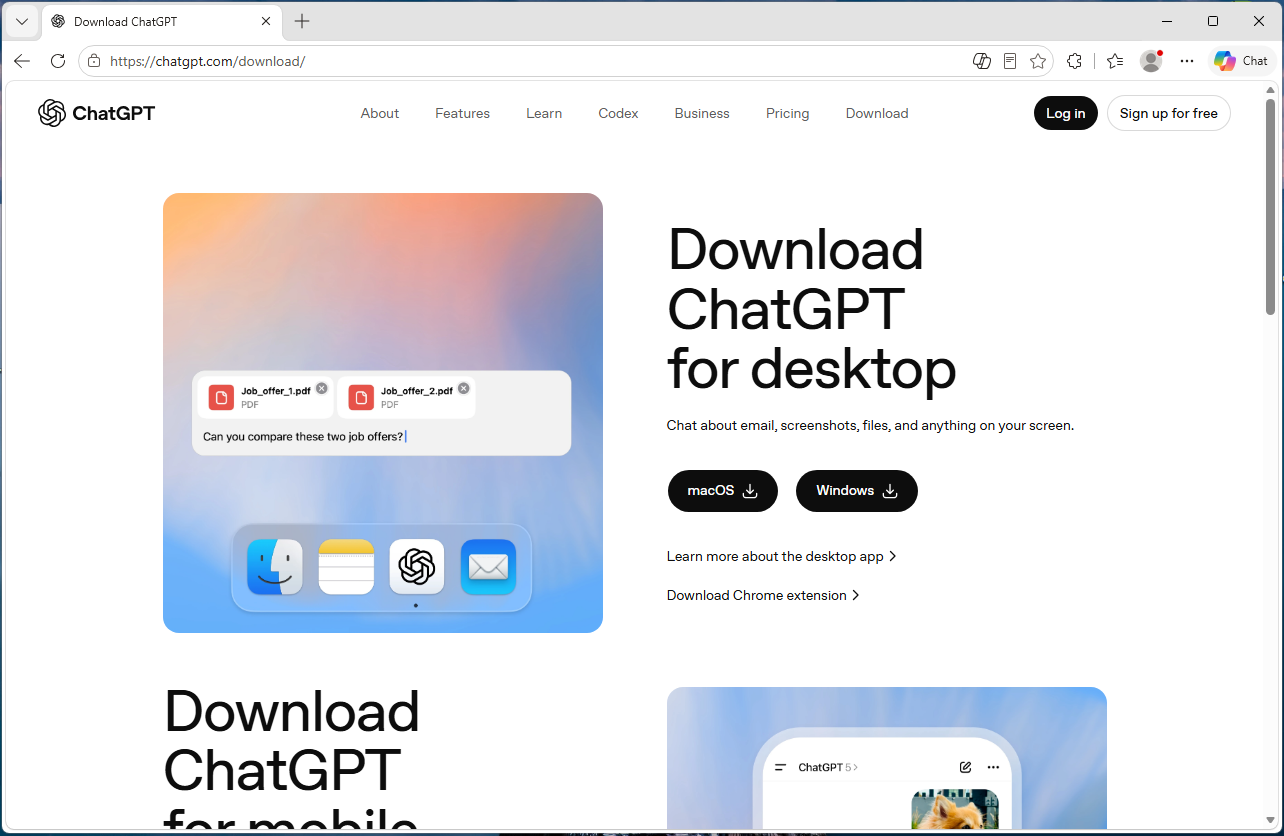
Searching for ChatGPT? This fake download site serves malware to both Windows and Mac users, using separate payloads tailored to each platform.…
Read More
CIOs rushing to roll out AI agents without real visibility into their decision-making processes are flirting with disaster. According to AI experts, deploying agents without observability processes an…
Read More
Mechanical hands dexterous enough to thread a needle, childlike dancing robots and adult-sized ones to help with deliveries were on display Thursday as the Humanoids Summit Tokyo opened.…
Read More
For decades, cybersecurity was a battle of skill. Elite attackers versus elite defenders. The rules of engagement were understood, even if the playing field wasn’t level. If you hired better analysts …
Read More
A new campaign orchestrated by a previously undocumented threat actor has targeted cryptocurrency organizations with an aim to facilitate digital asset theft using recruitment-themed social engineerin…
Read More
Federal prosecutors on Wednesday charged a Google employee with insider trading on Polymarket. In a seven-page complaint filed in federal court in the Southern District of New York (SNDY), the Departm…
Read More
Online or telephone IT support scams have been tricking employees into downloading or clicking on malware for years. But according to the FBI, one group that targets US-based law firms has recently fo…
Read More
A robot being developed at Duke University is almost ready to face the world, in any direction.…
Read More
Over the next three to five years, both governments and the private sector will need to rapidly adapt identification and mitigation protocols as adversaries move from AI-assisted to AI-enabled sanctio…
Read More
The U.S. said Wednesday that it was “disappointed” in a decision by the Dutch government to block New York-based Kyndryl’s planned acquisition of a cloud services provider over concerns about national…
Read More
SpaceX Starship launches are on hold pending an investigation into last week's test flight.…
Read More
CISOs relying on LLM runtime guardrails and official safety scores when making security decisions about their organizations’ AI usage and model selection are due for a wakeup call. According to a new …
Read More
A new phishing tool is allowing cyber attackers to get access to Microsoft 365 users' accounts without even needing to know your password, the FBI said in a warning issued to the public on Thursday.…
Read More
The Federal Aviation Administration (FAA) has ordered SpaceX to investigate the cause of its Starship booster losing control and crashing into the Gulf of Mexico during a test flight last week, the ag…
Read More
Sen. Elizabeth Warren (D-Mass.) is calling for an overhaul of the U.S. tax code to tax artificial intelligence companies, arguing the gains from AI should "benefit all Americans." "Building an economy…
Read More
An adversary could transform the digital footprints created by modern smartphones into grid coordinates, which can then be used to target U.S. troops with deadly precision, the head of U.S. Special Op…
Read More
NASA is paying two companies millions to provide specialized lunar vehicles to help support the agency's moon base missions.…
Read More
Massachusetts became the first state to certify that ride-hailing drivers with Uber and Lyft, who are considered independent contract workers under federal law, can organize and form a union. Ride-hai…
Read More
Many seniors struggle with health apps and portals despite wanting to use them. Learn how to overcome digital health literacy barriers and stay safe.…
Read More
Artificial intelligence is "an unstoppable force" that is being weaponized in ways that fall just short of traditional warfare, Britain's cyberspying chief warned Wednesday.…
Read More
Latin America and Europe become the target of two banking trojan campaigns that are designed to infect Windows and Android devices with Grandoreiro and BTMOB malware, respectively. That's according to…
Read More
The typical CEO compensation package rose nearly 6% in 2025 to $17.7 million, as company boards rewarded their top executives for bigger profits and higher stock prices, and gave them incentives to st…
Read More
Cybersecurity researchers have discovered a new malicious package on the npm registry that comes with information stealing capabilities. According to OX Security, the package, named "mouse5212-super-f…
Read More
President Trump has appointed former Attorney General Pam Bondi to his panel on science and technology, nearly two months after he fired her as the head of the Department of Justice. Bondi will serve …
Read More
A single malformed character in a web request can let an unauthenticated attacker slip past the access controls that guard applications built on Starlette, the open-source Python framework that powers…
Read More
When an employee installs an AI writing assistant, connects a coding copilot to their IDE, or starts summarizing meetings with a new browser tool, they are doing exactly what a productive employee sho…
Read More
Bank security codes sent via text may not be enough. Learn why authenticator apps and passkeys offer stronger two-factor authentication protection.…
Read More
CrowdStrike, in partnership with Google and the Shadowserver Foundation, has announced the simultaneous disruption of all command-and-control (C2) channels associated with GlassWorm, a persistent soft…
Read More
Most organizations still picture cyber defense as a fortress problem: build stronger walls, add more guards, buy another detection engine. But modern incidents rarely crash through the front gate. The…
Read MoreThe FBI has warned that attackers are using a new phishing kit to gain long-term access to Microsoft Outlook, Teams, and OneDrive accounts.…
Read More
A SpaceX Falcon 9 rocket is displayed at a SpaceX facility in Hawthorne, Calif., on April 2, 2026. (Mario Tama/Getty Images)…
Read More
Cybersecurity researchers have disclosed a security flaw in Gitea, an open-source, self-hosted platform for version control, that allows unauthenticated remote attackers to pull private container imag…
Read MoreCox Media said it could spy on users through their devices and use the information for targeted advertising, except it wasn't true.…
Read More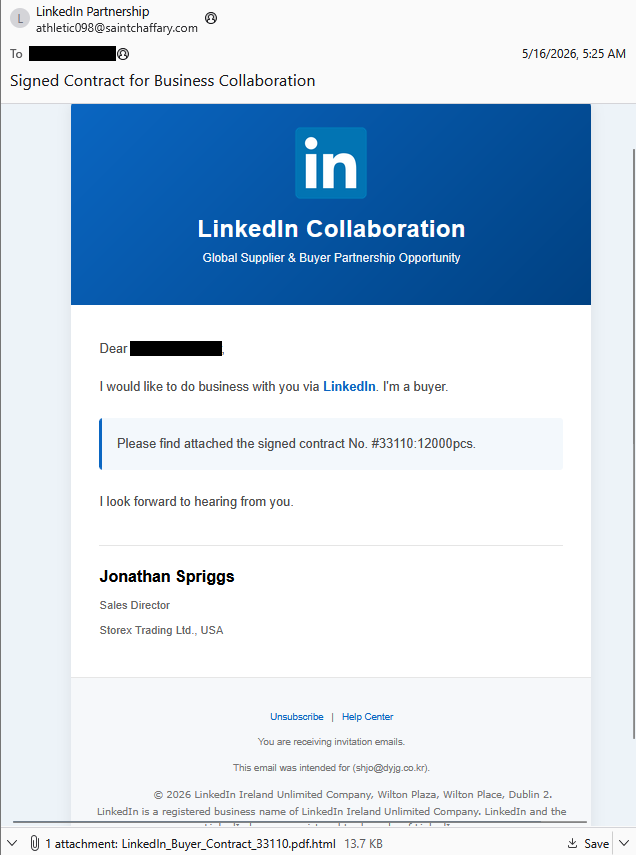
Phishers are stealing LinkedIn credentials while abusing Adobe Target to track victims and redirect them to real LinkedIn pages.…
Read More
For most of my career running security operations, the shape of cyber conflict has been defined by who could move faster than the other side. Faster at identifying a vulnerability, faster at patching,…
Read More
Microsoft has warned of an active cryptojacking campaign that makes use of artificial intelligence (AI) chatbot interactions as a mechanism for surfacing malicious download sites. "This emerging deliv…
Read More
Data security posture management (DSPM) explained Data security posture management (DSPM) tools help security teams examine their entire data environment to find shadow data, reducing the risk of data…
Read More
An American Airlines jet lands at Ronald Reagan Washington National Airport outside Washington on Jan. 31, 2025. (Jeenah Moon/Reuters)…
Read More
Are Apple devices spying on you? Learn how Siri listens, what data gets collected and the privacy settings you should change on your iPhone today.…
Read More
The Iranian hacking group known as MuddyWater has been linked to a new campaign affecting at least nine organizations across nine countries on four continents in the first quarter of 2026. The activit…
Read More
Over 2.6 million Do Not Call complaints were filed with the FTC, with robocalls dominating. Here are the top states affected and how to stay safe.…
Read More
We found fake installers and plugins for ChatGPT, Claude, AutoTune, and other popular software that can give attackers full control over your device.…
Read More
Every single day, hackers are finding new ways to crash websites and steal data. But right now, something has changed. Hackers are no longer working alone. They are now using powerful Artificial Intel…
Read More
Microsoft has rolled out updates to fix a remote code execution vulnerability impacting SharePoint that could be exploited by bad actors in attacks without requiring any specialized conditions to be m…
Read More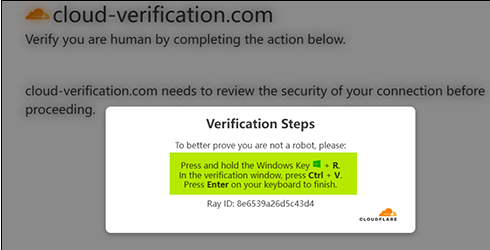
Hackers are abusing a Ghost CMS website flaw to serve fake Cloudflare verification pages that pressure users into infecting their own PCs.…
Read More
Multi-factor authentication (MFA) was supposed to close a critical gap in identity security. It meant that, even if an attacker possessed the account credentials, they couldn't log in without the seco…
Read More
The Indian Computer Emergency Response Team (CERT-In) has issued new guidelines requiring organizations to patch critical security vulnerabilities in internet-exposed systems within 12 hours of being …
Read More
The Iranian state-sponsored threat actor known as Nimbus Manticore (aka Screening Serpens and UNC1549) has been attributed to a fresh campaign using lures impersonating organizations in the aviation a…
Read More
A now-patched high-severity security flaw affecting Digital Knowledge KnowledgeDeliver, a Learning Management System (LMS) popular in Japan, was exploited as a zero-day to deliver the Godzilla web she…
Read More
Veterans reported $419 million in fraud losses in 2024 as scammers exploit military records and VA data. Here are the biggest scams and how to fight back.…
Read More
LaGuardia Airport debuts a life-sized AI hologram named Bridget in Terminal B, offering travelers conversational directions to gates, lounges and baggage claim.…
Read More
Monday recap. Same mess, new week. A sketchy dev tool got people pwned, old bugs came back from the dead, and security products somehow needed protecting from themselves. A bunch of companies spent th…
Read More
Authorities in the Netherlands have arrested the co-owners of two related Internet hosting companies for operating IT infrastructure used by Russia to carry out cyberattacks, influence operations and …
Read More
Threat actors are exploiting a recently disclosed critical security flaw in Ghost CMS to inject malicious JavaScript code with an aim to fuel ClickFix attacks. According to QiAnXin XLab, the activity …
Read More
Ask a cybersecurity pro about Network Detection and Response (NDR) and you might still hear "Noisy," "Too much data." But ask the teams running NDR that includes agentic AI capabilities and you'll hea…
Read More
Cybersecurity researchers have shed light on a cross-platform malware called RemotePE that has been put to use by the North Korea-linked Lazarus Group in attacks targeting financial and cryptocurrency…
Read More
A new coordinated cross-ecosystem software supply chain attack campaign has targeted npm, PyPI, and Crates.io to distribute credential-stealing malware. The campaign, codenamed TrapDoor, spans more th…
Read More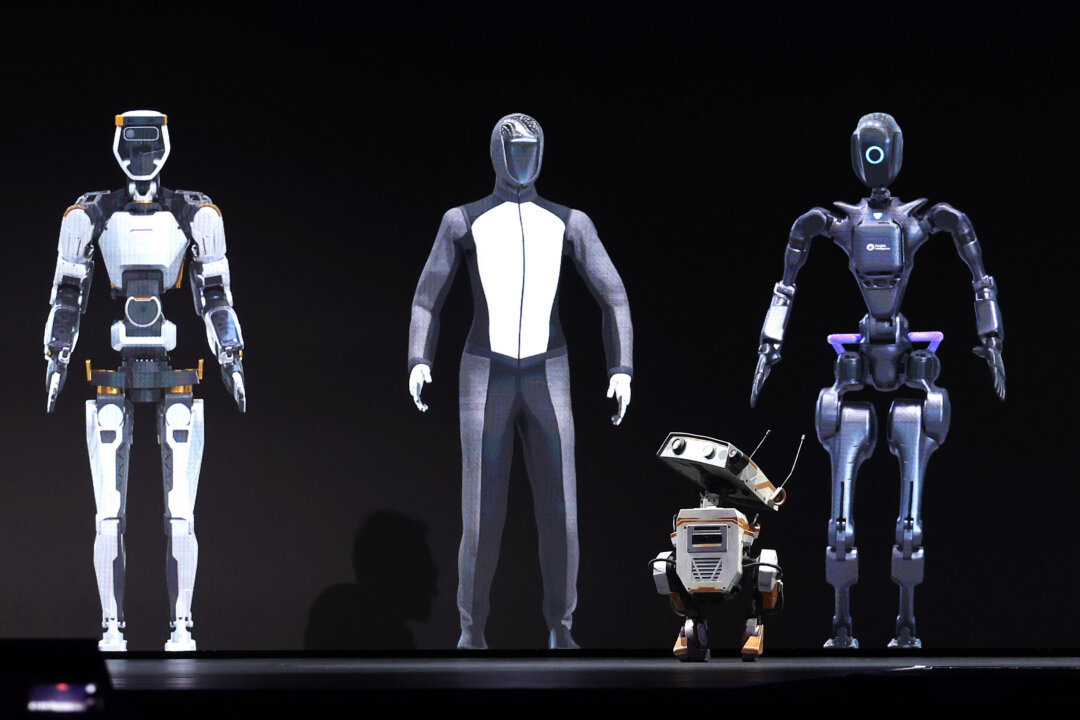
Robots appear on stage during the Nvidia GTC Artificial Intelligence Conference in San Jose, Calif., on March 18, 2024. (Justin Sullivan/Getty Images)…
Read More
Figure AI claims its three humanoid robots completed over 24 hours of continuous autonomous package sorting without any human control in a warehouse test.…
Read More
Fake CAPTCHA scams trick users into opening command windows and pasting malicious scripts, installing StealC malware that steals passwords silently.…
Read More
A pro-democracy protester using a laptop computer as he sits on an occupied road in the Admiralty district of Hong Kong early on Oct. 8, 2014. (Ed Jones/AFP via Getty Images)…
Read More
A security researcher says Yarbo robot mowers contained serious flaws enabling remote access, live camera feeds and Wi-Fi password theft from home networks.…
Read More
Credit freezes block many fraudulent applications but miss synthetic identity fraud, account takeovers and tax refund scams. Here is what else to do.…
Read More
GitHub has rolled out new controls for npm to improve the security of the software supply chain, giving maintainers the ability to explicitly approve a release prior to the packages becoming publicly …
Read More
A new "coordinated" supply chain attack campaign has impacted eight packages on Packagist including malicious code designed to run a Linux binary retrieved from a GitHub Releases URL. "Although the af…
Read More
Anthropic on Friday disclosed that Project Glasswing has helped uncover more than 10,000 high- or critical-severity vulnerabilities across some of the most "systemically" important software across the…
Read More
Cybersecurity researchers have flagged a fresh software supply chain attack campaign that has targeted multiple PHP packages belonging to Laravel-Lang to deliver a comprehensive credential-stealing fr…
Read More
A maximum-severity security vulnerability impacting LiteSpeed User-End cPanel Plugin has come under active exploitation in the wild. The flaw, tracked as CVE-2026-48172 (CVSS score: 10.0), relates to …
Read More
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added a recently patched critical security flaw impacting Drupal Core to its Known Exploited Vulnerabilities (KEV) catalog, based o…
Read More
Authorities in Europe and North America have announced the dismantling of a criminal virtual private network (VPN) service used by criminal actors to obscure the origins of ransomware attacks, data th…
Read More
Lawmakers in both houses of Congress are demanding answers from the U.S. Cybersecurity & Infrastructure Security Agency (CISA) after KrebsOnSecurity reported this week that a CISA contractor intention…
Read More
A convincing inheritance scam email targets victims with fake deadlines and official-looking language. Learn how to spot it and protect your personal data.…
Read More
The Belarus-aligned threat actor known as Ghostwriter (aka UAC-0057 and UNC1151) has been observed using lures related to Prometheus, a Ukrainian online learning platform, to target government organiz…
Read More
Oscar-nominated filmmaker Paul Schrader says his artificial intelligence girlfriend dumped him, plus more stories in the Fox News AI Newsletter.…
Read More
This Chrome update fixes critical flaws attackers could exploit through malicious websites, but not the “Browser Fetch” vulnerability.…
Read More
Cybersecurity researchers have disclosed details of a new automated campaign called Megalodon that has pushed 5,718 malicious commits to 5,561 GitHub repositories within a six-hour window. "Using thro…
Read More
1 Introduction This article provides a technical analysis of how many Windows kernel mode drivers can be interacted with from user mode without the hardware they were developed for. This work was moti…
Read More
About 80% of companies deploying AI reported workforce reductions, but Gartner says those cuts did not translate into stronger returns on investment.…
Read More
The U.S. Department of Justice (DoJ) on Thursday announced the arrest of a Canadian man in connection with allegedly operating a distributed denial-of-service (DDoS) botnet known as Kimwolf. In tandem…
Read More
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday added two security flaws impacting Langflow and Trend Micro Apex One to its Known Exploited Vulnerabilities (KEV) catalog, …
Read More
Cisco has rolled out updates for a maximum-severity security flaw impacting Secure Workload that could allow an unauthenticated, remote attacker to access sensitive data. Tracked as CVE-2026-20223 (CV…
Read More
An Apple logo at an Apple store in Paris on April 23, 2025. (Abdul Saboor/Reuters)…
Read More
The logo of social network X displayed on a smartphone in Brussels on Sept. 27, 2024. (Nicolas Tucat/AFP via Getty Images)…
Read More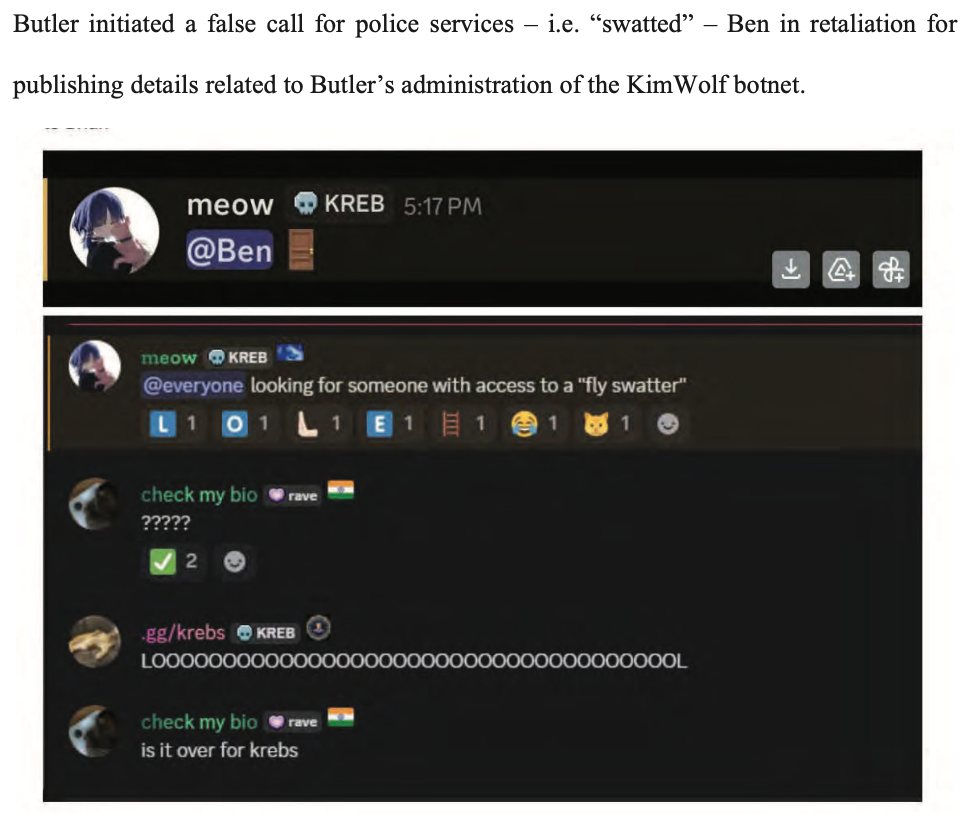
Canadian authorities on Wednesday arrested a 23-year-old Ottawa man on suspicion of building and operating Kimwolf, a fast spreading Internet-of-Things botnet that enslaved millions of devices for use…
Read More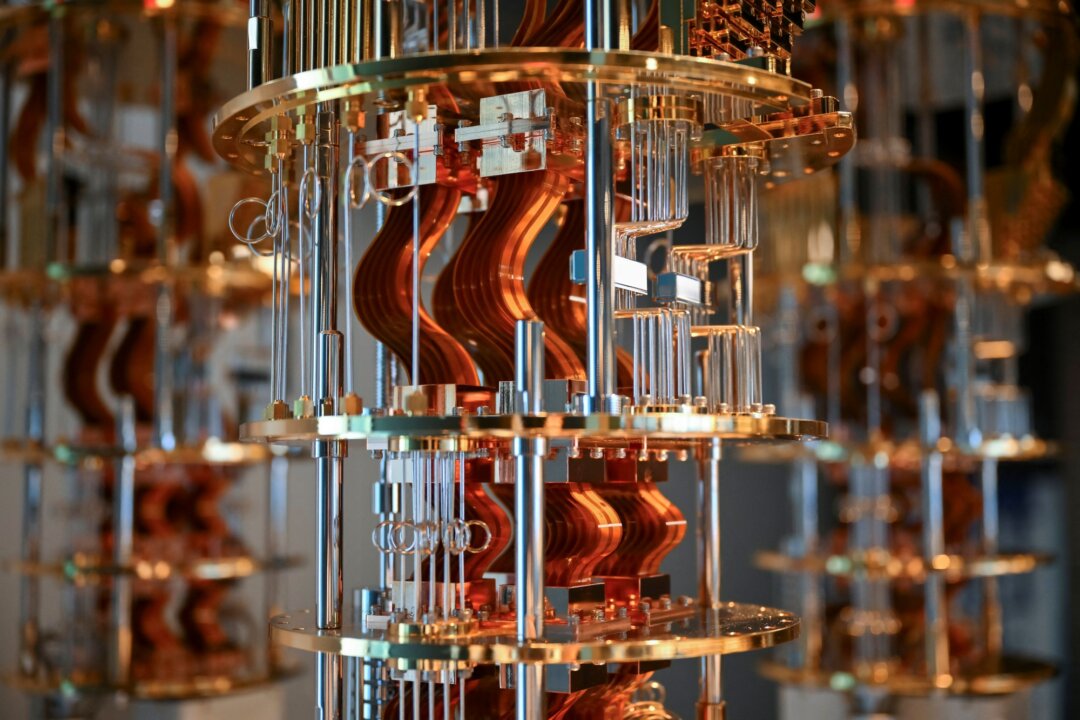
Parts of the IBM Quantum System Two are displayed at IBM Thomas J. Watson Research Center in Yorktown Heights, N.Y., on June 6, 2025. (Angela Weiss/AFP via Getty Images)…
Read More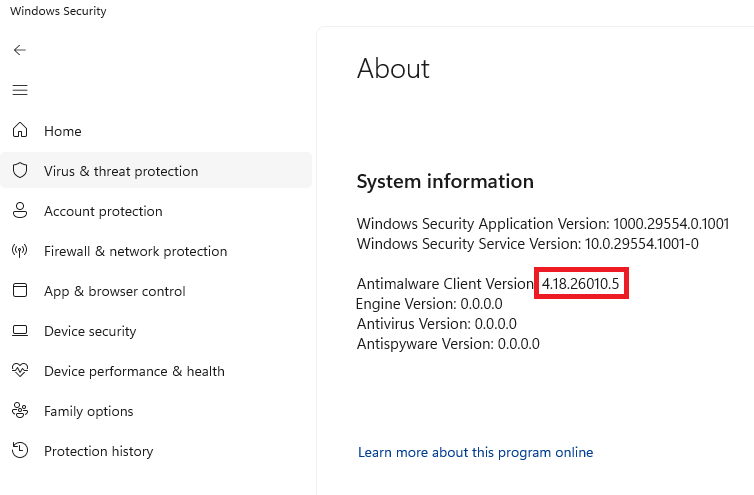
CISA added seven known exploited vulnerabilities to its KEV catalog, including two Microsoft Defender flaws.…
Read More
A fraudulent Geek Squad billing email using Razorpay branding is pressuring consumers to click payment links and hand over sensitive personal information.…
Read More
Cybersecurity researchers have disclosed details of a new Linux malware dubbed Showboat that has been put to use in a campaign targeting a telecommunications provider in the Middle East since at least…
Read More
This week starts small. A token leaks. A bad package slips in. A login trick works. An old tool shows up again. At first, it feels like the usual mess. Then you see the pattern: attackers are not alwa…
Read More
Microsoft has disclosed that a privilege escalation and a denial-of-service flaw in Defender has come under active exploitation in the wild. The former, tracked as CVE-2026-41091, is rated 7.8 on the …
Read More
Meta says Incognito Chat is coming to WhatsApp and the Meta AI app, offering temporary AI conversations processed in a secure environment that even Meta cannot access.…
Read More
Consider a cached access key on a single Windows machine. It got there the way most cached credentials do - a user logged in, and the key stored itself automatically. Standard AWS behavior. No one mis…
Read MoreKnow when a program tries to access your webcam so you can allow or block, in real time.…
Read More
Cybersecurity researchers have disclosed details of a vulnerability in the Linux kernel that remained undetected for nine years. The vulnerability, tracked as CVE-2026-46333 (CVSS score: 5.5), is a ca…
Read More
Treasurer Jim Chalmers speaks during Question Time at Parliament House in Canberra, Australia, on May 13, 2026. (Hilary Wardhaugh/Getty Images)…
Read More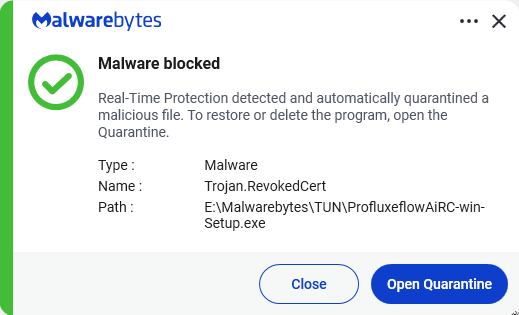
The service let malware authors sign malicious files with fraudulent Microsoft-issued certificates to bypass security checks.…
Read More
Gail Barr was tricked into paying $9,260 through a Bitcoin ATM in a jury duty scam on her 70th birthday. Arizona's new crypto kiosk law saved her.…
Read More
Medicare scam ads on Facebook allegedly reached older Americans with fake benefit offers, a new CCDH report claims. Meta says it fights scams hard.…
Read More
Firefox 151 adds major privacy improvements and fixes high-priority security vulnerabilities, making this an update you shouldn’t ignore.…
Read More
Julie Inman-Grant, Australia's eSafety Commissioner speaking at an official function to mark the start of Australia's social media ban at the prime minister's official residence, Kirrilbilli House, in…
Read More
Unitree says its GD01 rideable robot starts at $574,000, walks on two legs, transforms into four-legged form and can smash through a pile of bricks.…
Read More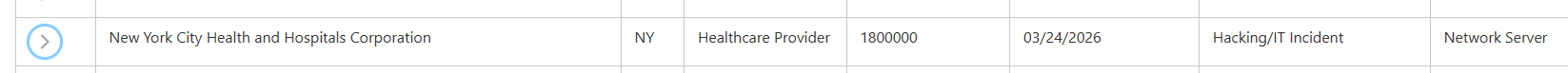
NYC Health + Hospitals says attackers accessed its systems for months through a third-party vendor compromise, affecting at least 1.8 million people.…
Read More
Turning 65 can trigger data brokers to sell your personal details to marketers and scammers. Learn how to protect yourself before Medicare enrollment.…
Read More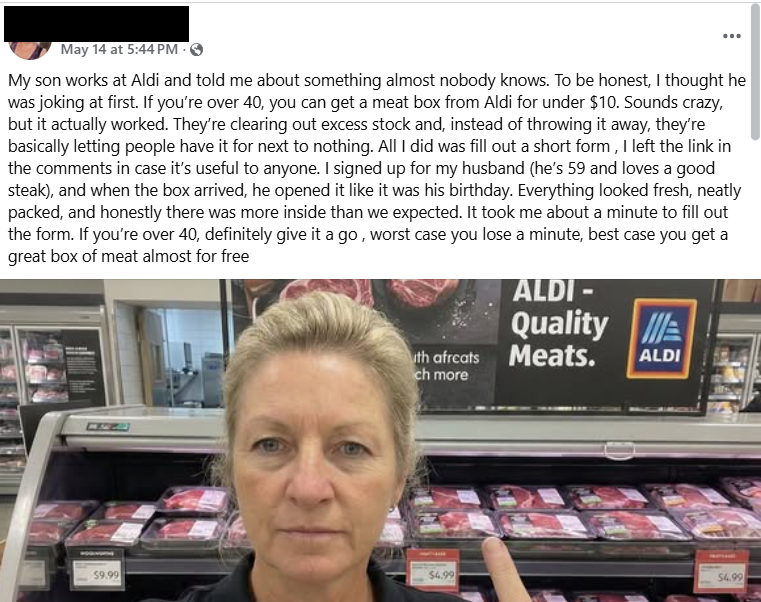
A fake Aldi “meat box” offer spreading on Facebook tricks victims into handing over personal and payment info.…
Read More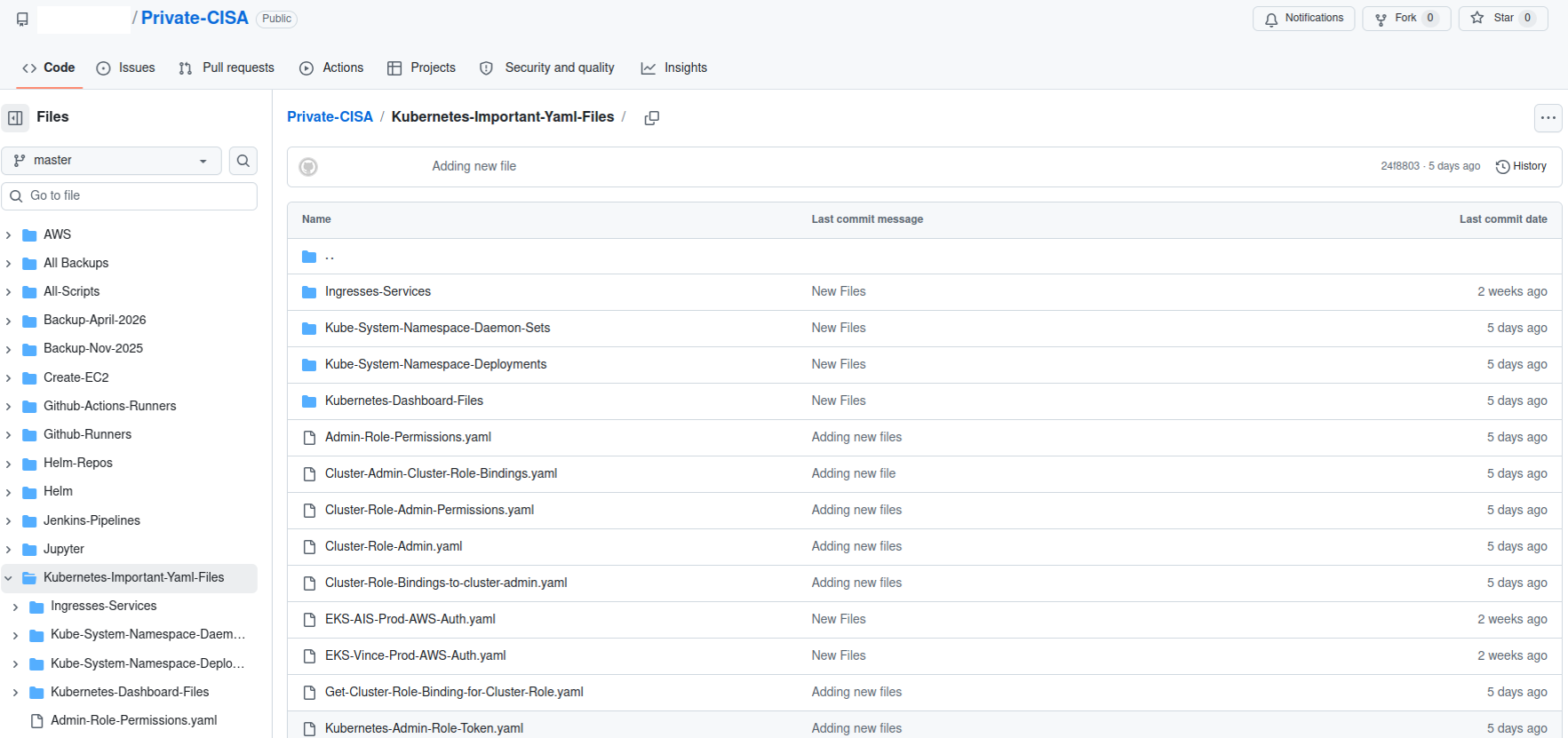
Until this past weekend, a contractor for the Cybersecurity & Infrastructure Security Agency (CISA) maintained a public GitHub repository that exposed credentials to several highly privileged AWS GovC…
Read More
Scammers are sending fake Amazon product recall texts with phishing links designed to steal your login and payment details. Here's how to spot them.…
Read More
OpenAI logo in this illustration taken May 20, 2024. (Dado Ruvic/Illustration/Reuters)…
Read More
An employee holds a silicon wafer with chips etched into it at Applied Materials in Sunnyvale, Calif., on May 22, 2023. (Jim Wilson/Pool/AFP via Getty Images)…
Read More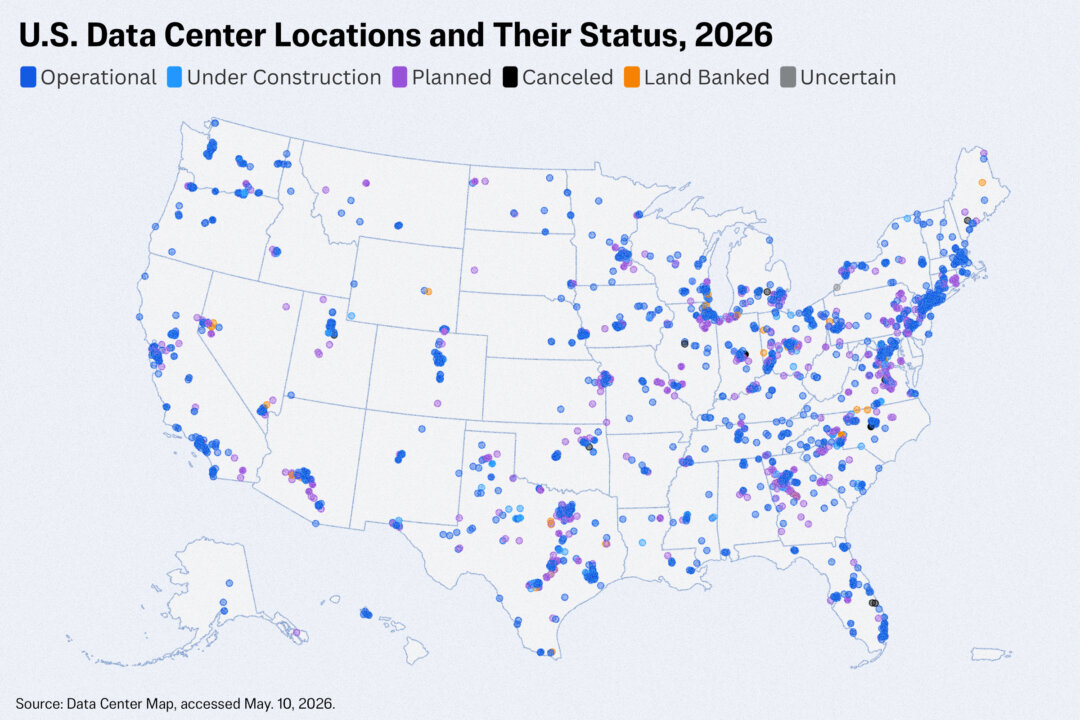
No content available…
Read More
Elon Musk looks on as US President Donald Trump speaks at the US-Saudi Investment Forum in Washington, DC, on Nov. 19, 2025. (Brendan Smialowski/AFP via Getty Images)…
Read More
President Donald Trump (L) listens as Nvidia CEO Jensen Huang speaks in the Cross Hall of the White House during an event on "Investing in America" in Washington, on April 30, 2025. (Andrew Harnik/Get…
Read More
OpenAI CEO Sam Altman arrives at the Ronald V. Dellums Federal Building in Oakland, Calif., on April 30, 2026. (Benjamin Fanjoy/Getty Images)…
Read More
Instagram, TikTok, Snapchat, YouTube, Facebook, Twitch, and Reddit applications are displayed on a mobile phone on Dec. 9, 2025. (Hollie Adams/Reuters)…
Read More
Microsoft CEO Satya Nadella arrives to court at the Ronald V. Dellums Federal Building in Oakland, Calif., on May 11, 2026. (Benjamin Fanjoy/Getty Images)…
Read More
An ongoing data extortion attack targeting the widely-used education technology platform Canvas disrupted classes and coursework at school districts and universities across the United States today, af…
Read More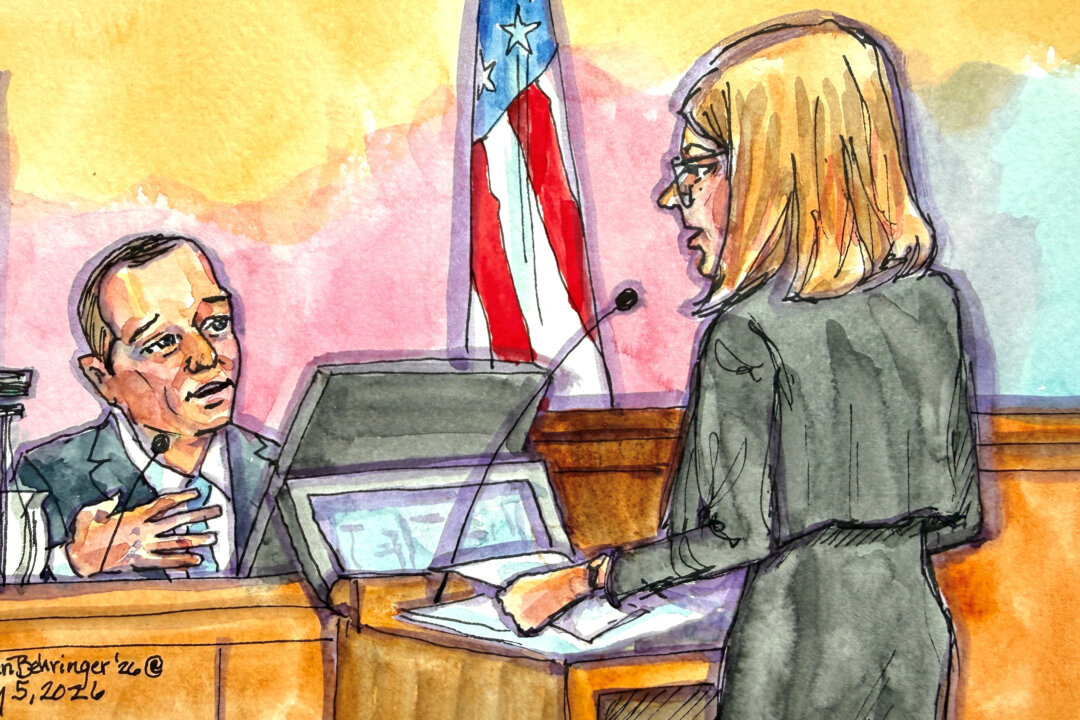
OpenAI President Greg Brockman is depicted in a courtroom sketch as he is questioned by OpenAI attorney Sarah Eddy, during Elon Musk's lawsuit trial over OpenAI's for-profit conversion at a federal co…
Read More
The logos of Google, Apple, Facebook, Amazon, and Microsoft displayed on cellphone and laptop screens. (Justin Tallis/AFP via Getty Images)…
Read More
Secretary of War Pete Hegseth during a news briefing at the Pentagon in Arlington, Va., on April 24, 2026. (Madalina Kilroy/The Epoch Times)…
Read More
A Brazilian tech firm that specializes in protecting networks from distributed denial-of-service (DDoS) attacks has been enabling a botnet responsible for an extended campaign of massive DDoS attacks …
Read More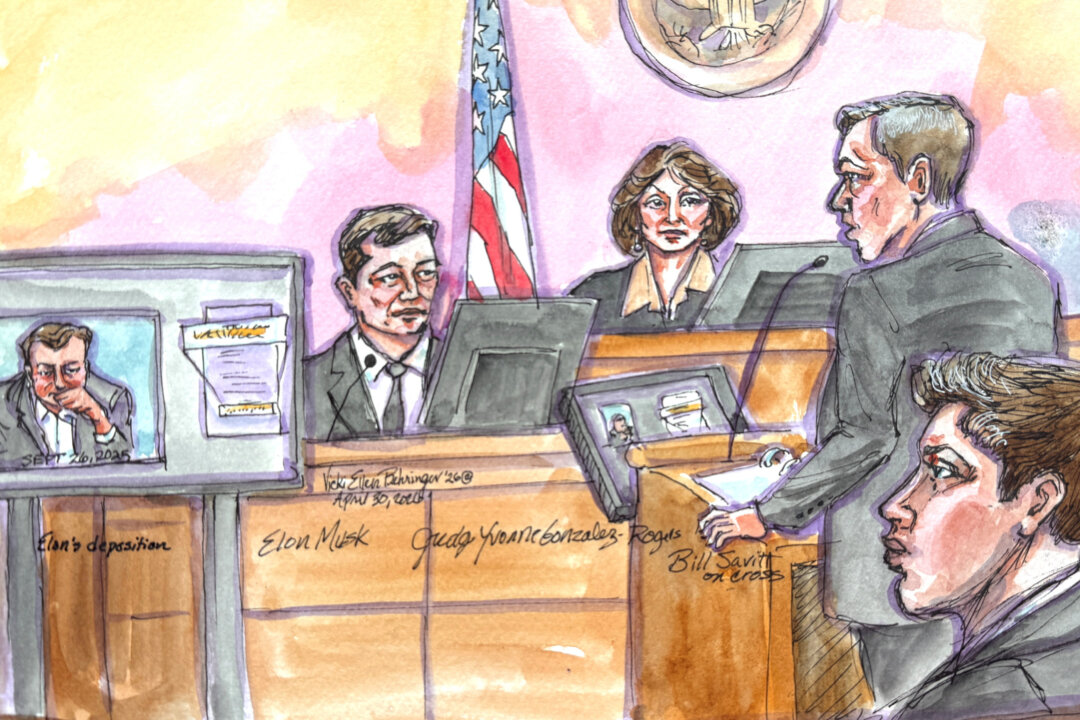
OpenAI attorney William Savitt cross-examines Elon Musk as his deposition is played on a screen, during Musk's lawsuit trial over OpenAI's for-profit conversion before U.S. District Judge Yvonne Gonza…
Read More
Social media apps displayed on a mobile phone screen on Jan. 3, 2018. (Yui Mok/PA)…
Read More
Shoppers at a grocery store in Centreville, Va. on Nov. 2, 2025. (Madalina Kilroy/The Epoch Times)…
Read More
Technology company Meta Platforms at a booth during the AI+Expo Special Competitive Studies Project in Washington on June 2, 2025. (Madalina Vasiliu/The Epoch Times)…
Read More
A computer with the OpenAI logo is staged on a gradient blue background with the shadow of a man in the background in Grenoble, France, on Feb. 12, 2025. (Anouk Anglade/Hans Lucas/AFP via Getty Images…
Read More
A teenager uses her mobile phone to access social media in New York City on Jan. 31, 2024. (Spencer Platt/Getty Images)…
Read More
Chairman and CEO of Microsoft Satya Nadella speaks on stage during the Microsoft AI Tour at TikTok Entertainment Centre in Sydney, Australia on April 23, 2026.(George Chan/Getty Images)…
Read More
A school within the Los Angeles Unified School District in Los Angeles on Jan. 8, 2024. (John Fredricks/The Epoch Times)…
Read More
An American flag waves in front of NASA’s Vehicle Assembly Building at Kennedy Space Center, Florida, on Feb. 19, 2026. (T.J. Muscaro/The Epoch Times)…
Read More
A close-up view of the Telegram messaging app is seen on a smartphone in London on May 25, 2017. (Carl Court/Getty Images)…
Read More
Employees work on a production line of drones intended for export at a factory in Ruichang, Jiangxi Province, China, on Nov. 27, 2024. (STR/AFP via Getty Images)…
Read More
A 24-year-old British national and senior member of the cybercrime group "Scattered Spider" has pleaded guilty to wire fraud conspiracy and aggravated identity theft. Tyler Robert Buchanan admitted hi…
Read More
The Uber logo is shown on a building in Los Angeles on Feb. 14, 2024. (Mike Blake/Reuters)…
Read More
A Blue Origin New Glenn rocket lifts off from the Cape Canaveral Space Force Station in Cape Canaveral, Fla., on April 19, 2026. (Reuters/Joe Skipper)…
Read More
A technician works at an Amazon Web Services AI data center in New Carlisle, Ind., on Oct. 2, 2025. (Noah Berger/Getty Images via Amazon Web Services)…
Read More
Microsoft today pushed software updates to fix a staggering 167 security vulnerabilities in its Windows operating systems and related software, including a SharePoint Server zero-day and a publicly di…
Read More
Anthropic logo is seen in an illustration photo. (Dado Ruvic/Reuters)…
Read More
(Illustration by The Epoch Times, Getty Images)…
Read More
The Apple logo during the preview of the redesigned and reimagined Apple Fifth Avenue store in New York City on Sept. 19, 2019. (Brendan McDermid/Reuters)…
Read More
A pedestrian walks in front of the Meta logo at the Facebook headquarters in Menlo Park, Calif., on Oct. 28, 2021. (Justin Sullivan/Getty Images)…
Read More
Original hacker image by baramee2017 via Depositphotos. Composite image by The Epoch Times.…
Read More
Hackers linked to Russia's military intelligence units are using known flaws in older Internet routers to mass harvest authentication tokens from Microsoft Office users, security experts warned today.…
Read More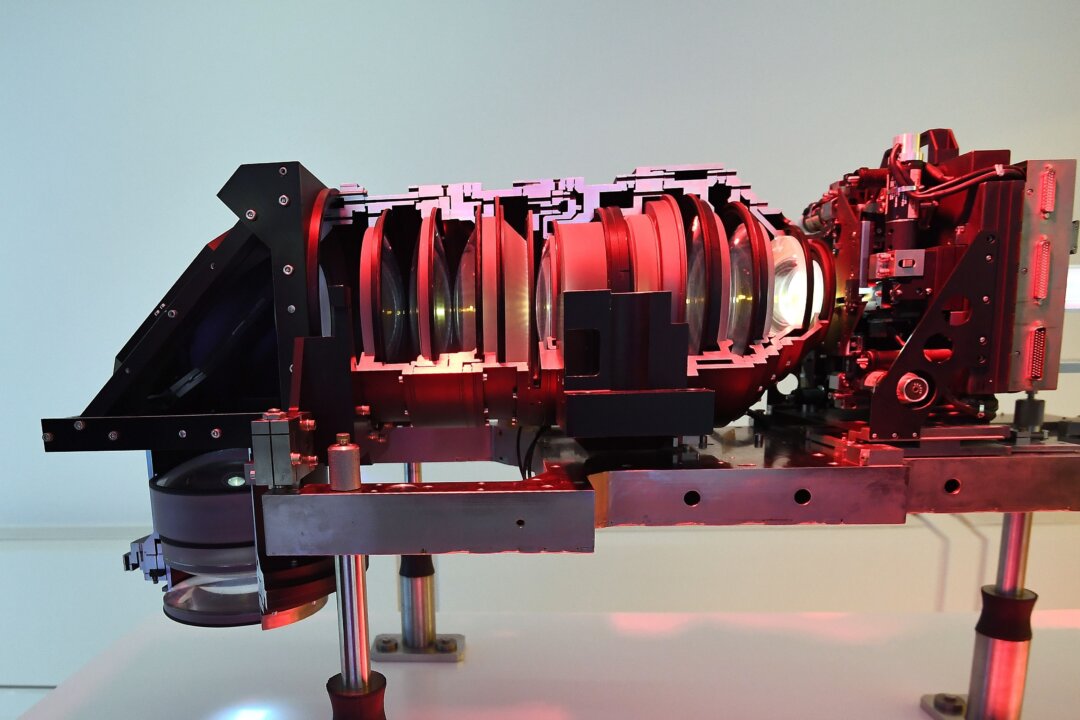
A lens used in the manufacturing of semiconductor circuits at ASML, a Dutch company that is currently the largest supplier in the world of semiconductor manufacturing machines via photolithography sys…
Read More
In this photo illustration, a hacker types on a computer keyboard on May 13, 2025. (Oleksii Pydsosonnii/The Epoch Times)…
Read More
This photograph shows a figurine in front of the logo of the U.S. artificial intelligence safety and research company Anthropic during a photo session in Paris on Feb. 13, 2026. (Joel Saget/AFP via Ge…
Read More
California Gov. Gavin Newsom speaks to reporters in Stockton, Calif., on Oct. 22, 2025. (Justin Sullivan/Getty Images)…
Read More
Australia’s eSafety Commissioner Julie Inman Grant addresses the National Press Club in Canberra, Australia on June 24, 2025. (AAP Image/Lukas Coch)…
Read More
The skyline of San Francisco on March 25, 2024. (John Fredricks/The Epoch Times)…
Read More
A boy poses for a photo while holding a game pad in front of a screen displaying the logo of the children's gaming platform Roblox, in this illustration taken on Dec. 8, 2025. (Ramil Sitdikov/Illustra…
Read More
President Donald Trump steps off Marine One as he returns to the White House on March 18, 2026. (Andrew Harnik/Getty Images)…
Read More
A 14-year-old boy poses at his home near Gosford as he looks at social media on his mobile phone in New South Wales, Australia, on Oct. 24, 2025. (David Gray/AFP via Getty Images)…
Read More
A photo shows a frame of a video generated by a new artificial intelligence tool, dubbed "Sora," unveiled by the company OpenAI, in Paris on Feb. 16, 2024. (Stefano Rellandini/AFP via Getty Images)…
Read More